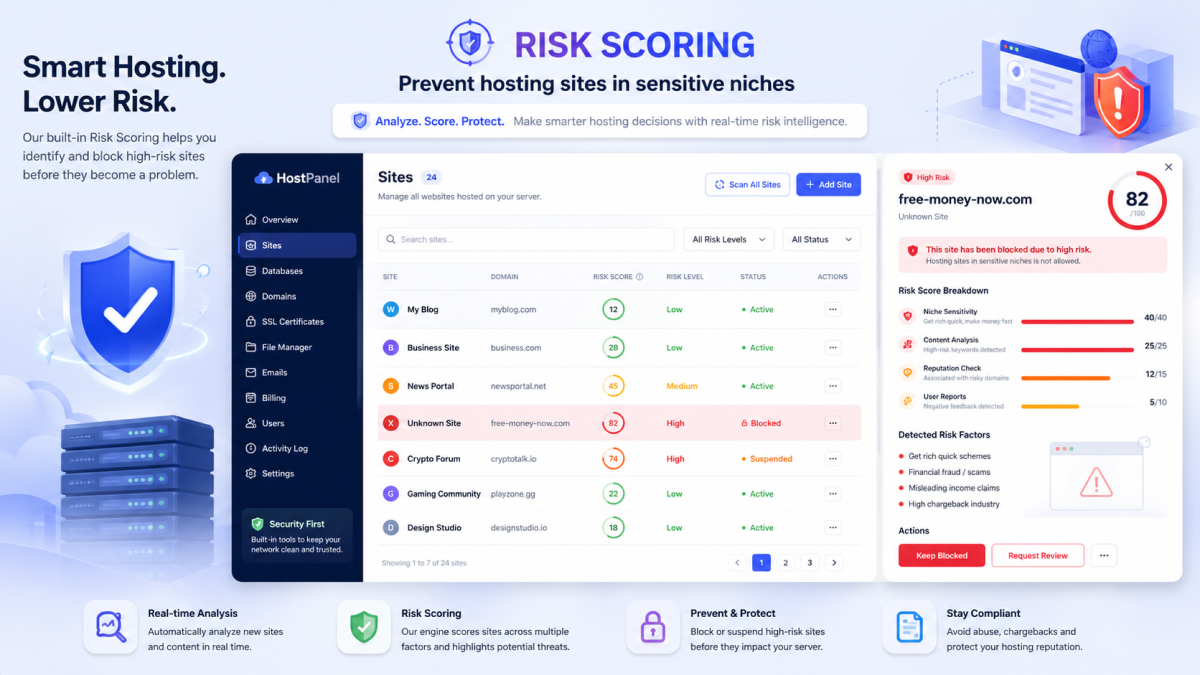
Managing Risk-Sensitive Sites with Web-CP. Risk Scoring, CAPTCHA, and Bot Defense in Practice
Operators of high-risk websites — online gambling, adult content, crypto on-ramps, file-sharing portals, fintech, betting affiliates, dating, and large user-generated platforms — share a common technical reality: they attract a disproportionate volume of automated traffic, fraud attempts, credential stuffing, and abuse before a single legitimate user signs in. For these operators, security is not a quarterly project — it is a daily operational discipline that begins at the hosting layer.
This article examines how a PHP-based control panel like Web-CP can be configured to harden risk-sensitive sites in production. Where our previous post on building anti-abuse systems covered detection and reporting workflows, this one focuses on the preventive layer: risk scoring, CAPTCHA integration, traffic shaping, and tenant isolation — the controls that stop bad traffic before it ever reaches the application.
The Risk Surface in Sensitive Niches
Sites in sensitive niches face a wider and more aggressive threat surface than typical hosting tenants. The most common categories include:
Credential stuffing and brute-force logins — driven by leaked password lists and rotating residential proxies
Sign-up fraud — disposable emails, voice-OTP bypass, and bonus-abuse rings (especially in iGaming and fintech)
Scraping and content theft — odds feeds, casino databases, adult catalogs, and pricing data are constantly mirrored
Payment fraud and chargeback farming — synthetic identities funneling through checkout flows
Spam and SEO injection — comment forms, registration endpoints, and contact pages weaponized for backlinks
DDoS and Layer-7 floods — targeted at login, search, and game-launch endpoints during peak hours
What makes these threats different from generic web threats is volume and persistence. A risk-sensitive site does not see one attack per week — it sees automated probes every minute, and its defensive posture must reflect that.
Risk Scoring as the First Line of Defense
Rather than treating every visitor identically, modern hosting stacks aggregate signals into a numeric risk score that drives downstream decisions: allow, challenge, throttle, or block. Web-CP supports this approach by exposing the signals it already collects to scoring rules and external engines.
Input Signals
A practical risk-scoring pipeline draws on:
IP reputation — ASN, datacenter vs. residential origin, presence on RBL/DNSBL lists
Geographic context — country, mismatch between billing and connection geo, sanctioned jurisdictions
Behavioral signals — request rate, mouse and keyboard entropy, headless-browser fingerprints
Account history — prior chargebacks, deposit/withdrawal velocity, device fingerprint reuse
Network-level signals — TLS fingerprint (JA3/JA4), HTTP/2 frame ordering, header anomalies
Scoring in Practice
Each signal contributes weighted points. A simple example expressed as Apache environment variables, populated from a Web-CP-managed configuration:
SetEnvIf X-Forwarded-For "^(1\.2\.3\.|5\.6\.7\.)" risk_ip=40
SetEnvIf User-Agent "(curl|python-requests|Go-http-client)" risk_ua=30
SetEnvIfNoCase Geo-Country "RU|KP|IR" risk_geo=25
# Aggregate at the application layer
RewriteCond %{ENV:risk_ip} ^[3-9][0-9]$ [OR]
RewriteCond %{ENV:risk_ua} ^[3-9][0-9]$
RewriteRule ^/(login|signup|checkout) /challenge.php [L]Scores above a tunable threshold trigger a challenge page; scores in the high band trigger an outright block and a Web-CP audit-log entry. The same scoring output can be exported to the abuse pipeline so that repeat offenders accumulate evidence over time.
Where Web-CP Fits
Web-CP itself is not a fraud engine, but it provides the plumbing that scoring engines need:
Per-domain Apache and Nginx templates where rules can be deployed consistently
Centralized environment variable injection across VirtualHosts
Log aggregation per domain account, ready for ingestion by SIEMs or fraud platforms
A reseller-aware permission model so regional operators can tune their own thresholds without breaking global policy
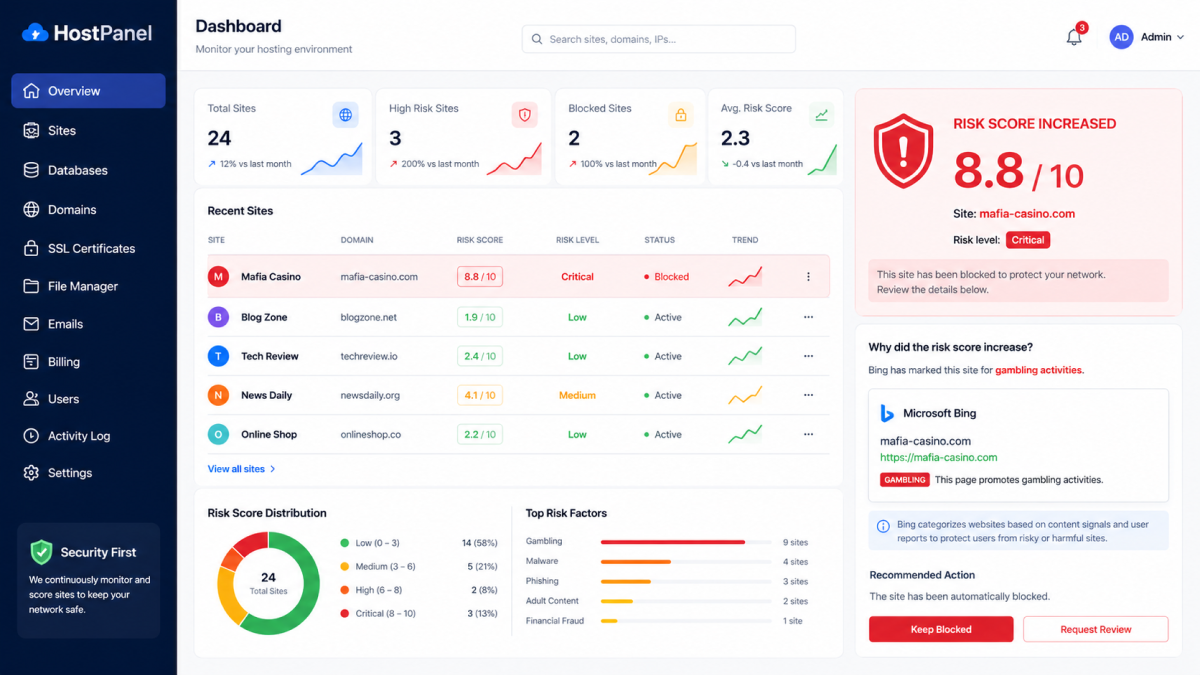
A Business View of the Score
Risk scoring is usually framed as a defensive control, but operators in sensitive niches quickly find a second use for it: a clean, classified view of who is actually visiting the site. Once scraper traffic, residential-proxy fraud, and headless bots are separated from the rest, what is left is the real picture — including how often Googlebot, Bingbot, and other major crawlers reach the site, which pages they fetch, and how their behavior shifts after content or technical changes.
"For us in the iGaming space, SEO traffic is everything — but reading what the search engines are actually doing has always been hard, because Googlebot and Bingbot get lost in a fog of scrapers and proxy farms pretending to be them. Web-CP's risk scoring cleaned that up. The first month we turned it on, we could see exactly how often Google was crawling our review pages versus our terms-and-conditions pages, and how Bing's pattern shifted after a sitemap update. From a business perspective, the score dashboard is now one of our SEO instruments, not just a security tool."
— Head of Growth, Mafia Casino site
For an operator, that classified traffic stream is also the cleanest possible read on how search engines are treating the site. Sudden drops in Googlebot crawl frequency, or a Bingbot pattern that ignores newly published categories, become visible business signals rather than noise buried under automated traffic. Verified-crawler counts, broken out by user-agent and reverse-DNS-checked origin, effectively become an SEO health gauge that sits next to the security dashboard.
CAPTCHA and Bot Mitigation at the Panel Layer
CAPTCHA is the most visible bot-defense mechanism, but in risk-sensitive niches a single CAPTCHA flow is rarely enough. Web-CP supports a tiered challenge model where the friction shown to a user scales with their risk score.
Challenge Tiers
Invisible challenge — passive scoring (e.g., reCAPTCHA v3, hCaptcha Enterprise, Turnstile) for the bottom 90% of traffic
Interactive challenge — image or puzzle CAPTCHA for medium-risk traffic
Proof-of-work — client-side computational challenge for suspected bot networks; cheap for humans, expensive at scale
Step-up authentication — email or SMS verification for high-risk sessions touching financial endpoints
Integration Points
CAPTCHA should be placed everywhere automated abuse is profitable, not only at the public login form:
Public site — registration, login, password reset, contact, comment, and search endpoints
Personal control panel — Web-CP's own login, especially for accounts with shell or DNS privileges
Reseller and server panels — a stolen reseller credential can compromise hundreds of domains, so these flows benefit from the strictest tier
API endpoints — token-issuance endpoints, often missed in CAPTCHA rollouts
A practical Web-CP deployment ships with reCAPTCHA, hCaptcha, and Cloudflare Turnstile keys configured at the server-template level, then inherited by every reseller and domain unless explicitly overridden.
Server Panel Hardening
For the Web-CP control panel itself, recommended hardening for sensitive-niche operators includes:
Enforce CAPTCHA on every panel login attempt, not only after N failed tries
Require a step-up challenge for destructive actions (account deletion, DNS zone wipe, SSL key rotation)
Bind admin sessions to ASN, not just IP, to allow mobile use without weakening the trust model
Rotate API rate-limit keys per reseller to contain credential leaks
Rate Limiting and Traffic Shaping
Rate limiting is the unglamorous workhorse of bot defense. Without it, even a perfect CAPTCHA can be drained by an attacker willing to pay for solver services.
Web-CP exposes rate-limit primitives at three layers:
Per-IP — short-window limits on login, signup, and password reset (e.g., 5 attempts per 60 seconds)
Per-account — daily ceilings on sensitive actions (deposits, withdrawals, KYC submissions)
Per-resource — CPU and connection caps configured through the reseller panel, so a single compromised domain cannot starve neighbors
Example Apache configuration deployed via a Web-CP VirtualHost template:
<Location "/api/login">
SetHandler server-status
Require all granted
<IfModule mod_ratelimit.c>
SetOutputFilter RATE_LIMIT
SetEnv rate-limit 5
</IfModule>
</Location>Combined with mod_evasive or a sidecar service, this gives operators a workable baseline against the noisy 80% of automated abuse, freeing the scoring engine to focus on harder cases.
Tenant Isolation: Containing the Blast Radius
A risk-sensitive site rarely runs in a vacuum. Affiliates, regional mirrors, white-label tenants, and staff accounts often share infrastructure. When one of them is compromised, the question is not whether — it is how far the damage spreads.
Web-CP's top-down permission model is designed for exactly this situation:
Server admin controls what resellers may configure
Reseller controls what domain owners may configure
Domain owner controls what individual users may do
Personal users see only their own mailbox, files, and settings
In practice, this lets an operator running, say, a casino brand across twelve mirror domains set strict baselines centrally — mandatory CAPTCHA, mandatory 2FA, locked PHP versions, no shell access — while still letting regional teams iterate on content. If one mirror is compromised, the blast radius is bounded by the reseller's quota and permissions, not by the entire fleet.
Recommended baselines for sensitive-niche tenants:
Disable shell access by default; enable per-user only with audit
Lock PHP versions and disable dangerous functions (
exec,system,proc_open) at the template levelForce separate MySQL users per domain with no cross-database
GRANTRequire per-domain SSL via Let's Encrypt automation
Enable Web-CP's encrypted audit logs for every privileged action
Putting It Together: An Operational Workflow
A mature deployment combines the layers above into a single workflow:
Inbound request lands at the reverse proxy and is scored against IP, ASN, geo, and TLS fingerprint
Score routing sends low-risk traffic straight through; medium-risk traffic gets an invisible CAPTCHA; high-risk traffic gets an interactive challenge or block
Authenticated actions pass through per-account rate limits and step-up authentication on sensitive endpoints
Audit logging captures every decision into Web-CP's encrypted log store, where it feeds the abuse-reporting pipeline described in our earlier article
Policy review runs weekly: operators inspect the score distribution, false-positive rate, and CAPTCHA solve-rate, and tune thresholds in the reseller panel
This loop turns ad-hoc firefighting into a measurable defensive posture — which is what auditors, payment processors, and licensing authorities increasingly expect from operators in regulated niches.
Conclusion
For sites in sensitive niches, security cannot be an afterthought bolted onto the application. It has to live at the hosting layer, where every request is visible and every tenant is governed by the same baseline. Web-CP's combination of templated VirtualHosts, top-down permissions, integrated CAPTCHA hooks, rate-limit primitives, and audit logging gives operators the building blocks to deploy a defensible posture across an entire fleet — without writing a custom platform from scratch.
Risk scoring, CAPTCHA, and tenant isolation are not exotic features in 2026 — they are the baseline. Operators who treat them as first-class concerns, and who manage them through a unified control plane, will continue to operate reliably while their less-disciplined competitors burn cycles on incident response.